Managed Detection & Response
NuSpective delivers and manages the Technology and People to perform effective and affordable Compliance Monitoring and Cybersecurity Operations
Key Elements of our MDR Services include:
SIEM
Technology
Log
Analytics
24×7 Threat
Hunting
Incident
Remediation
Guidance
Compliance
Reporting
How NuSpective MDR Service Works with Your Team
to Reduce Your Cyber Risk and Ensure Compliance with Regulatory Requirements
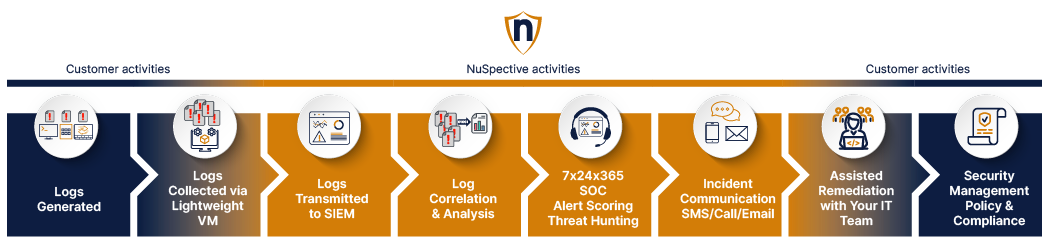
The diagram above depicts the typical chronological source and delivery flow of our MDR services.
- Blue boxes: Service aspects that are customer led activities
- Orange boxes: Service aspects that are NuSpective led activities
- Transitional Colored Boxes: Service aspects that are jointly (Customer and NuSpective) worked activities
MDR Advanced vs. MDR Platinum Comparison Chart
Product Features
MDR Advanced
MDR Platinum
FAQs
Frequently Asked Questions
-
There are other MDR Service Providers, why NuSpective?
At the foundational level, NuSpective prides itself on establishing and maintaining our business relationships to deliver honest, straightforward, and consistent solutions, and services, at every touch point. We are passionate about living in our “customer’s shoes” with a commitment to listening and responsiveness. With over 10 years in business, our customers continue to work with us because we operate with these values every day.
At the services level, NuSpective is committed to effective Compliance Monitoring and Cybersecurity Operations at a competitive price. Our staff experts are highly trained and 100% based in United States. NuSpective Fully Manages the Technology & People required to deliver comprehensive and compliant security operations. The service includes the SIEM licenses and underlying infrastructure. Your logs are Aggregated/Correlated enabling us to provide Customized Alerts Scoring & Prioritization. We staff our Cybersecurity Experts for 24×7 “eyes on glass” and execute complete daily reviews of High, Medium, and Low severity events and alerts. Your team will receive customized communication of all priority alerts as well as remediation support for actionable incidents. We pride ourselves on delivering highly customizable security operations services with attention to detail delivered with “white glove” treatment -
Where are your technicians based? Are they located outside of the United States?
100% of the NuSpective staff and SOC technicians are based in the United States and are English-speaking.
-
We already have log analytics tools, why NuSpective?
NuSpective Fully Manages the Technology & People required to deliver comprehensive and compliant security operations. The service includes the SIEM licenses and underlying infrastructure. Your logs are Aggregated/Correlated enabling us to provide Customized Alerts Scoring & Prioritization. We staff our Cybersecurity Experts for 24×7 “eyes on glass” and execute complete daily reviews of High, Medium, and Low severity events and alerts. Your team will receive customized communication of all priority alerts as well as remediation support for actionable incidents.
-
We already have Firewalls and End-Point Protection Technology in place, why NuSpective MDR?
Network firewalls and endpoint protection technologies provide the ability to see and respond to cybersecurity events; however, these technologies need to be monitored by the appropriate combination of technology and people to effectively protect your business against threats that can travel or multiply in your network. Furthermore, the method to stop an active cybersecurity threat is not always clear. NuSpective MDR manages and delivers trained experts and SIEM technology to execute the monitoring and remediation guidance that your organization needs to maximize the effectiveness of your cybersecurity tools.
-
What are the key differences between MDR Advanced and MDR Platinum?
MDR Advanced includes automated, technology-based 24×7 monitoring and alerting as well as a daily compliance review by a SOC Cybersecurity Analyst. Remediation guidance for MDR Advanced customers is delivered via email in the form of “Playbooks.” MDR Advanced is best for customers that need to ensure cybersecurity compliance with daily log reviews, but do not need to real time human-based alert response by our SOC team.
MDR Platinum includes everything in MDR Advanced, plus 24×7 real-time, people-based monitoring and alerting by trained SOC Cybersecurity Analysts. In the case of actionable incidents, our SOC experts will provide live remediation guidance support.
-
How does after hours support work? Can it be customized?
For both our MDR Services, technology-based Analytics and Alerting is performed and delivered on 24×7 basis. Additionally with our MDR Advanced service, 24×7 people-based coverage and support is available to your team. Our SOC team targets a 30-minute response time for high-severity and emergency incidents, we complete our investigation, confirm the incident, and contact your team via the communication method, and point of contact, of your choice (SMS/Email/Phone).
-
Can I customize my Alerting and Communication Process?
Absolutely! Tuning alerts is a critically important feature of our service. With your input, we customize the alerting, scoring and escalation procedures to eliminate false negatives and minimize false positives. For both MDR Advanced and MDR Essentials customers, our SOC team will work with you during the onboarding process to tune the alerts accordingly. Furthermore, we support on-going SIEM configuration changes to continually improve how we alert and communicate with your team.
For MDR Advanced customers, our team will additionally document and maintain a customized SIEM “runbook” to ensure it evolves as your business processes and people change. This is designed to accommodate your changing IT environment, and to improve the means (time of day, escalation contacts, etc.) by which we communicate with your team.
-
How is remediation defined?
Remediation is the effort and expertise applied to abate the impact of actionable security incidents.
Our MDR Advanced service provides people-based guided remediation; our SOC analyst assisting your IT team with expert recommendations, instructions, and best practice methodologies to stop and/or mitigate the incident.
Remediation included with the MDR Essentials service is automated and emailed remediation “playbooks.” Our “playbooks” are designed to provide best practices recommendations and instructions to guide your internal staff with necessary steps to stop and/or mitigate the incident.
-
Can I use NuSpective MDR to monitor end points like laptops/desktops?
Yes, you can use NuSpective MDR to monitor laptops or desktops. There are several ways to make this process efficient and affordable; our team can help you determine the best method for your organization.
-
Do NuSpective MDR Services also include End-Point Detection & Response (EDR)?
While our MDR Service options do not currently include EDR, we do have expertise in helping you design and implement an EDR Solution for your business; we can then offer our MDR Service to collect and examine the aggregate EDR log source.
-
How does NuSpective MDR work with Public Cloud Infrastructure?
The log collector VM can be easily installed in AWS, Azure, GCP (or essentially any public cloud) to ingest logs from your public cloud virtual machines and virtual network devices. NuSpective MDR service can also ingest infrastructure logs from the aggregated log sources such as CloudTrail from AWS.
-
What does Compliance Automation Mean?
NuSpective MDR services are designed to make your life easier when it comes to cybersecurity compliance. With over 3,314 reports available out-of-the-box, NuSpective MDR service can provide you with weekly automated compliance reports.
Both MDR Advanced and MDR Essentials services include a log event review process performed every day by our SOC personnel, satisfying those regulatory or compliance requirements for daily log review.
-
How do logs get from our servers to the SIEM?
For private and public cloud environments a lightweight “log collector” VM is installed in your datacenter environment; the log collector receives logs from any source (virtual or physical) with an IP Address. Examples: network devices, virtual and/or physical servers, cloud VM’s, etc. Normally, your VMs and devices send the logs directly to our Managed SIEM via HTTPS encrypted outbound connections.
For SaaS environments (Example: Microsoft Office 365) we configure logs to be sent directly from the SaaS application to the Managed SIEM via encrypted connections (varies per SaaS application).
-
Does a VPN need to be set up?
The log collector does not require any VPN connection and does not require any inbound firewall ports to be opened.
-
How are log sources counted with aggregate servers?
An aggregate server is treated as a single log source, in rare instances additional charges for excess logs for a monthly billing cycle may apply. We will ensure that your expectations are properly set if this is anticipated.
-
Will NuSpective have access to my systems?
NuSpective staff members will not have access to any of your systems. Our SOC team will have the ability to send “commands” to the log collector installed in your environment. The log collector is a SIEM log collector VM that is security hardened and used widely in high-security environments such as banking, healthcare, and government.
-
Is NuSpective’s SIEM technology homegrown?
No, the SIEM element of our MDR service is supported using Fortinet’s FortiSIEM product (formally AccelOps).
-
How will NuSpective support post event forensics, and security posture improvements?
Beyond the guided remediation that our SOC team provides, there are multiple ways that NuSpective can support post-event clean-up.
During an event, NuSpective has immediate access to high-value cybersecurity remediation teams that can start working your problem in a matter of hours, not days. Emergency service can be costly, but we have access to capable, emergency-ready resources should you need it.
Following an event, we assist your team in assessing your cybersecurity posture, establishing a gap analysis, and planning for improvements.
-
Does NuSpective MDR services include a Configuration Management Database (CMDB)?
Yes, the CMDB provides critical “expected behavior context.” This particular feature of our SIEM tool covers the following: device configuration, OS version, interfaces and protocols, installed applications, running processes, and patch levels. In addition, it provides User Identity Mapping and Reporting and Geolocation Tracking for all traffic. It uses context-aware rules, based on the database, to only detect applicable incidents. This is a key feature in eliminating “false positives”.
Get Quote
Get a simple, straightforward quote!

Want To Learn More?
Meet with Us
Meet with our experts!



